Over the last couple of years, evolving technology, increased threat vectors and growing attacker sophistication have driven up the frequency and severity of cyber incidents, causing a rise in cyber insurance claims and subsequent underwriting losses. As a result of this volatile risk environment, most policyholders have faced continued premium hikes.
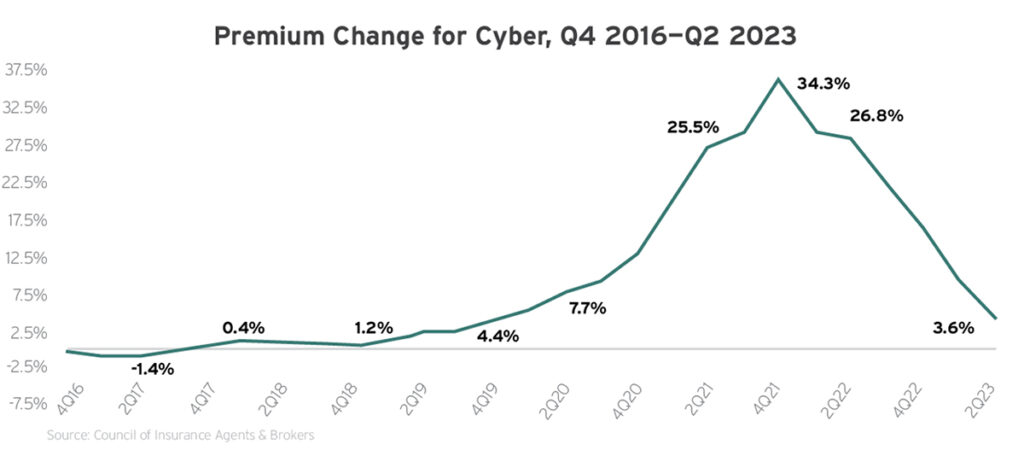
Specifically, industry data found that average cyber insurance rate increases peaked at 34% in the fourth quarter of 2021 and remained in double digits for the entirety of 2022. Fortunately, the segment experienced underwriting profitability in 2022, allowing for market conditions to soften throughout 2023. As such, industry research confirmed that most policyholders encountered more modest, single-digit rate increases this past year; according to Zywave’s latest Hard Market Conditions Pulse Survey, more than half (62%) of insurance brokers and agents saw their clients’ cyber insurance premiums decline, remain flat or rise by less than 10% in 2023.
Despite rate deceleration trends across the segment, it’s worth noting that many insureds are still experiencing widespread coverage restrictions, further scrutiny from underwriters regarding cybersecurity practices and exclusions for losses stemming from certain events (e.g., incidents involving the wrongful collection of data, cyberwarfare and ransomware). Furthermore, some policyholders with elevated cyber exposures continue to face double-digit rate jumps.
Moving into 2024, industry experts anticipate that market conditions will likely keep softening, albeit at a slower pace than in 2023. Nevertheless, this segment sees frequent changes and reacts to such developments faster than other lines of coverage, making pricing predictions difficult to pin down. More than anything, policyholders with a strong cybersecurity posture and a deep understanding of the current threat landscape will be best equipped to navigate the coming year’s cyber insurance market. This means that insureds who fail to adopt proper cybersecurity protocols or experience a rise in cyber losses may encounter ongoing premium hikes and coverage restrictions for the foreseeable future.
2024 Price Prediction: 0% to +15%
Developments and Trends to Watch
Data collection concerns
A growing number of businesses have begun leveraging biometrics, pixels and other tracking technology to gather personal information from stakeholders for various HR, advertising and marketing processes; however, doing so poses several data privacy concerns. For instance, businesses that neglect to comply with applicable international, federal and state legislation (e.g., The General Data Protection Regulation, the Health Insurance Portability and Accountability Act, the Biometric Information Privacy Act and the California Privacy Rights Act) when collecting, processing and storing stakeholders’ data could face substantial regulatory penalties, costly lawsuits and associated cyber losses. Compounding concerns, cyber insurance carriers are increasingly excluding coverage for losses caused by the wrongful collection of data, leaving businesses largely unprotected against this exposure. With this in mind, it’s critical for businesses that leverage tracking technology to maintain compliance with relevant data privacy laws and prioritize obtaining stakeholders’ consent before using their personal information, thus keeping associated cyber losses to a minimum.
AI exposures
While AI technology can certainly offer benefits in the realm of cybersecurity—streamlining threat detection capabilities, analyzing vast amounts of data and automating incident response protocols—it also has the potential to be weaponized by cybercriminals, therefore exacerbating cyber losses and related claims among businesses. In particular, cybercriminals can utilize AI technology when creating and distributing malware, cracking passwords, deploying social engineering scams, identifying software vulnerabilities and analyzing stolen data. This technology can enable such activities to be carried out faster and with greater success rates, allowing cybercriminals to cause major damage and even evade detection. One of the most significant risks associated with AI technology in the hands of cybercriminals is the ability to formulate persuasive phishing messages with minimal effort, making these scams much more prevalent. For example, cybercriminals can use AI-powered chatbots to impersonate legitimate sources, such as banks and other businesses, to trick unsuspecting individuals into sharing sensitive information. To help combat losses stemming from weaponized AI technology, some businesses have begun implementing more comprehensive cybersecurity measures, particularly as it pertains to threat identification and data protection initiatives (e.g., updated security software, advanced access controls and routine employee training).
War exclusion considerations
Nation-state cyberattacks remain a top concern in the cyber insurance space, especially as geopolitical challenges (e.g., the Russia-Ukraine conflict) contribute to global cyberwarfare worries. According to a recent report from the World Economic Forum, 93% of cybersecurity experts and 86% of corporate executives said they believe geopolitical instability will likely cause a catastrophic cyberattack in the coming years. Complicating matters, coverage for cyberwarfare has become more difficult to secure. Namely, international insurance marketplace Lloyd’s of London issued a bulletin in August 2022 requiring its insurers to revise their standalone cyber insurance policies’ war exclusions to specifically prohibit coverage for “losses arising out of war and cyber operations that are a part of war.” These requirements went into effect on March 31, 2023. Lloyd’s of London pushed for this modernized war exclusion language in an effort to minimize systemic losses from cyberwarfare across the insurance industry, but it has proven challenging to obtain a market consensus on such language. In any case, as nation-state cyberthreats and associated losses continue to become more prevalent, additional carriers are likely to follow in Lloyd’s of London’s footsteps and implement updated war exclusions to shield themselves against large-scale payouts better.
Ransomware threats
Ransomware attacks, which entail cybercriminals compromising devices or servers and demanding large payments be made before restoring the technology (as well as any data stored on it), have skyrocketed over the past decade. These attacks impact businesses of all sizes and sectors, especially small- and medium-sized establishments. What’s worse, these attacks often carry costly losses—as a result of both substantial payment demands and technology and data recovery efforts. According to industry data, ransomware incidents jumped by nearly 400% between 2019 and 2021 before slightly cooling off in 2022. Yet, 2023 saw a resurgence in these attacks; a recent survey conducted by IT company Sophos found that such incidents increased by 47% in the first quarter of the year alone, while the average ransom payment increased by 55% during the same period. The survey also revealed that 40% of businesses affected by ransomware attacks in 2023 issued payments of $1 million or more to the perpetrators, up from just 11% in 2022. Looking ahead, research and market intelligence firm Cybersecurity Ventures confirmed that ransomware incidents will cost businesses up to $265 billion annually by 2031, with a new attack happening approximately every two seconds. In light of increasing ransomware threats, many cyber insurance carriers have started implementing stricter underwriting standards and requiring policyholders to document cybersecurity practices aimed at mitigating these attacks before providing coverage, while some have excluded coverage for such incidents altogether.
Business email compromise (BEC) risks
BEC scams involve cybercriminals impersonating seemingly legitimate sources (e.g., senior-level employees, suppliers, vendors, business partners or other organizations) via email. Cybercriminals use these emails to gain the trust of their targets, tricking victims into believing they are communicating with genuine senders. From there, cybercriminals convince their targets to wire money, share sensitive information (e.g., customer and employee data, proprietary knowledge or trade secrets) or engage in other compromising activities. These scams are among the most expensive types of social engineering losses, and they have become a major threat to businesses across industry lines. According to the FBI, BEC scams have cost businesses $51 billion in exposed losses throughout the past decade. Making matters worse, these scams have seen a significant rise in recent years, with such incidents surging by 47% since 2020 and even outpacing malware attacks during the first half of 2023. Considering these trends, it has become all the more important for businesses to have precautions in place to prevent, detect and respond to BEC scams to keep related cyber losses at bay.
Tips for Insurance Buyers
- Work with your insurance professionals to understand the different types of cyber coverage available and secure a policy that suits your unique needs. Start renewal conversations early.
- Take advantage of loss control services offered by insurance carriers to help strengthen your cybersecurity measures.
- Focus on employee training to prevent cybercrime from affecting your operations. Employees should be aware of the latest cyberthreats (e.g., AI-powered attacks, cyberwarfare, ransomware and BEC scams) and ways to mitigate them.
- Keep organizational systems secure by utilizing a virtual private network, installing antivirus software and endpoint detection and response solutions, implementing firewalls and email authentication technology, restricting employees’ administrative controls and encrypting all sensitive data.
- Store backups of critical data in a secure, offline location to minimize losses in the event of a ransomware attack.
- Update workplace software on a regular basis to ensure its effectiveness and consider using a patch management system to assist with updates.
- Establish an effective, documented cyber incident response plan aimed at remaining operational and minimizing damages in the event of a data breach or cyberattack. Test this plan regularly by running through various scenarios with staff. Make updates to the plan as needed.
- Consult insurance professionals and legal counsel to determine your organization’s regulatory exposures in regard to applicable data protection and cybersecurity laws. Make compliance adjustments as needed.
- Develop workplace policies that prioritize cybersecurity, including an internet usage policy, a remote work policy, a bring-your-own-device policy and a data breach response policy.
- Be sure to consider potential nation-state threats when establishing your organization’s cybersecurity policies and protocols.



